This article will discuss the NIST 800-207 standard, ZTAA, and the Security Service Edge. We’ll also explain how zero-trust architecture can benefit organizations. Finally, here are some common examples of zero trust architecture. To learn more about the principles behind the definition of zero trust network access – Fortinet read this article.
NIST 800-207 standard
The NIST 800-207 standard for Zero Trust network security has become the de facto industry standard for zero-trust network access. In May 2021, the US government will mandate this new standard which is expected to become mandatory in the private enterprise by the same date. This standard is vendor-neutral and contains elements from several organizations to ensure compatibility with today’s evolving attacks and threats. It is also compatible with the cloud-first model.
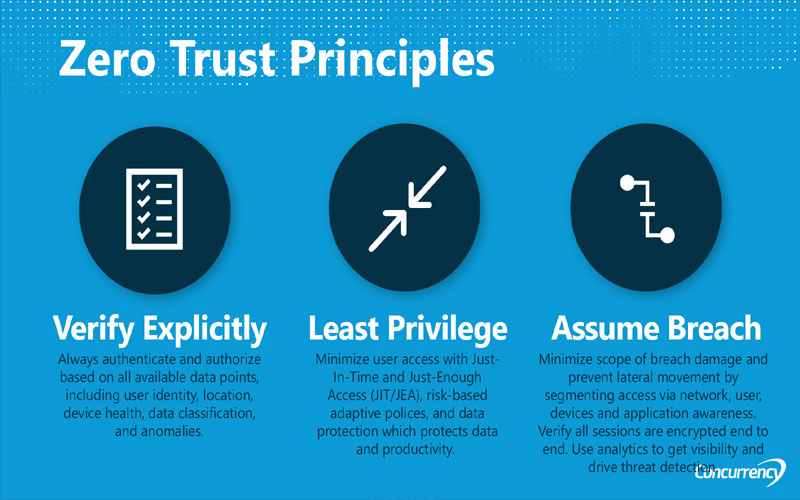
One of the guiding principles of Zero Trust security is the principle of least privilege. It requires users to limit the privileges of service accounts to those needed to complete a task. In addition, service accounts should have known behaviors and be assigned minimal connection privileges. Overly-permissive service accounts allowed attackers to move around the network by compromising domain controllers and authentication systems. When choosing a zero-trust solution for your network, there are seven critical questions.
ZTAA
One of the essential elements of Zero Trust network security is preventing lateral movement within an organization. Zero Trust works by assuming that a breach of a corporate firewall has already occurred and therefore verifies requests as if they came from an open network. The principles behind this model emphasize “never trust, always verify.” To accomplish this, administrators must implement appropriate authentication, authorization, and encryption controls to prevent and minimize lateral movement. Moreover, they must leverage analytics and rich intelligence to detect anomalies and threats.
Creating a Zero Trust architecture requires thorough knowledge of your network’s architecture. This includes all the physical and virtual assets, subjects, business processes, and other network components. Without a thorough understanding of your network’s structure, you will have blind spots and potentially unknown “shadow IT” components not identified by traditional security measures. A comprehensive network audit will uncover the proper steps to optimize your network for Zero Trust.
Security Service Edge
Using a comprehensive SSE solution provides secure remote access, monitoring user behavior, and control over access rights. Zero Trust Network Access (ZTNA) allows access to services only based on access control policies. ZTNA is based on network micro-segmentation and isolation. It is a VPN substitute that allows users to securely access business networks from multiple places and devices. While virtual private networks (VPNs) allow full access to LAN resources, zero-trust network access only provides access to those services to which a user explicitly grants access. One of the best online secure connection To understand how these two technologies work consider how they differ.
SSE (Security Service Edge) provides enterprise-grade security without tying users’ devices to the network. Instead, it delivers protection to any app or user on a secure cloud platform, regardless of location. Providing all security services from one platform eliminates network security gaps and improves visibility across users and data. In addition, it automatically enforces security updates, preventing users from becoming infected with malware.